Our latest puzzle was created by Eric Fulton, Sherri Davidoff, Jonathan Ham and Scott Fretheim.
“Oh god” is the first thought running through your mind as you crack open the door. An odious wafting of day old vomit, sweat, and stale cigar washes across you as the door moves from cracked to ajar. The room is pitch black, a dirty and exposed hallway light bulb does nothing to cut into the dark abyss of the room. Peering inside you see only shapes, but deep down you know it isn’t going to be pretty.
It’s been three weeks since the PaulDotCom crew went missing. Through extensive research and cyberstalking, millions of PDC fans gathered information relating to their disappearance and hired you to find them. This is John Strand’s safe house, and a quick Google image search was all you needed to know about his seedy life. Who knows what’s in this room? Donning rubber gloves you feel for a light switch with your left hand, both intensely afraid and curious for what you are about to see. Wincing in anticipation you flick the switch with a “clickâ€.
Nothing happens. “Why do I always get the messed up jobs” you whisper to yourself, digging around in your black bag. Corporate espionage isn’t a clean game, but usually the tech jobs involve threatening geeks in suburban houses, not sneaking around what looks to be North Dakotan project housing. Pulling a sleek Pelican flashlight from the bag, you click it on and begin to survey the damage. Starting from the left you identify the location of the puke smell; there’s day old vomit trailing its way down peeling wallpaper toward a box of empty tequila bottles. Smell one located.
Further to the right you spot a human shape on a couch. You freeze with the flashlight beam aimed at the shape. It’s Larry, wrapped in a dirty pink blanket almost too small to cover him, rocking back and forth and muttering something unintelligible. What’s he saying? You suspect it’s key. His fingers are pale as he grips a WRT54G router which appears to have twenty-four overlapping bites taken out of it. Seconds tick by. Nothing happens; he pays no attention to your entry. Smells two and three probably located. Your light continues its sweep as you spot a table hosting two 24†monitors surrounded by miscellaneous cables. Jackpot.
Ignoring the rest of the room you step over martini glasses and other unidentified objects, making a beeline to the desk. The little voice in your head shouts “Damn! Damn! Damn!” There is evidence that someone left only recently. The scene is almost out of a second rate Hollywood movie, being so incredibly obvious:a puddle of spilled cosmopolitan makes apparent the distinct outlines where a laptop and external hard drive once sat.
Disheartened, you rummage though the desk, hopeful of finding a forgotten USB drive or other storage device. No dice. You slide a few sticky quarters off of the desk (it’s not like you’re getting a per-diem) and continue the search– wait. One of the quarters… splits a little. You pick it up and play with it. Viola! A small micro SDHC card lies inside the quarter. Your heart starts beating faster. You have a clue.
As a matter of habit you go through the rest of the room, quietly, as the eerie sound of Larry chanting in the background never stops. Old coffee mugs, a dirty microwave, hundreds of empty frozen food wrappers, and magnetic buckyballs cover the floor like a sort of 21st century urban underbrush…and then you see something peculiar. A stack of hard drives sits in the corner. The top drive looks like someone shot it 7 or 8 times, a strange method for data destruction, but certainly an effective one. Rummaging through the stack of drives you find one at the bottom looking as if it survived the data massacre. Grabbing it, you give one last look around as you walk to the door. The sounds of Larry go from muffled to silent as you shut the door and make your exit.
The Evidence
You are the forensic investigator.The items found in the safe house have been uploaded to this server for your analysis. These include:
- quarter-SDHC-snippet.dd – A DD image of a the SDHC card found inside the quarter.
- pcap-from-surviving-hard-drive.pcap – A packet capture that you copied off the surviving hard drive.
Download the 7-zipped evidence file here.
SHA256 sum:
44450915addb8bdbe1766a3fad1c03059393a0f1f01839b19f98f235dc3b97bd
The Adoring Fans’ Questions
Can you solve the puzzle and find out what happened to PaulDotCom? Their adoring legions of fans have asked you to find the answers to the following questions along the way:
1. In his conversation with juniorkeyy, how old does Larry initially say he is?
2. What was the filename of the file that had the following SHA256 sum:
e56931935bc60ac4c994eabd89b003a7ae221d941f1b026b05a7947a48dc9366
3. What is the SHA256sum of the photo from the “dd” image that shows Larry taking a bite out of a wireless router?
4. What is the SHA256sum of the image that shows zombie Larry taking a
bite out of a cat?
5. What is Larry saying as he rocks back and forth? (No spaces or
capital letters.)
6. Where are Paul and John? Report their GPS coordinates:
a) Latitude
b) Longitude
BONUS. What is the name of the nearest bar?
Submission Form
Please submit your answers using the Official Submission Form.
Deadline is 7/23/12 (11:59:59PM UTC-11) (In other words, if it’s still 7/23/12 anywhere in the world, you can submit your entry.)
Prize
The Grand Prize will be a Black Hat “Black Card”! Thanks, Black Hat, for sponsoring such an awesome prize.
There will also be prizes for the first correct submission, as well as the 2nd and 3rd place runner-ups. Stay tuned for more info!
How to Win
The MOST ELEGANT solution wins. In the event of a tie, the entry submitted first will receive the prize. Coding is always encouraged. We love to see well-written, easy-to-use tools which automate even small sections of the evidence recovery. Graphical and command-line tools are all eligible. You are welcome to build upon the work of others, as long as their work has been released under a an approved Open Source License. All responses should be submitted as plain text. Microsoft Word documents, PDFs, etc will NOT be reviewed.
More Details
Feel free to collaborate with other people and discuss ideas back and forth. You can even submit as a team (there will be only one prize). However, please do not publish the answers before the deadline, or you (and your team) will be automatically disqualified. Also, please understand that the contest materials are copyrighted and that we’re offering them publicly for the community to enjoy. You are welcome to publish full solutions after the deadline, but please use proper attributions and link back. If you are interested in using the contest materials for other purposes, just ask first.
Authors agree that their code submissions will be freely published under the GPL license, in order to further the state of network forensics knowledge. Exceptional submissions may be used as examples and tools in the Network Forensics course or book. All authors will receive full credit for their work.
To Recap
Evidence File
Sha256sum: 44450915addb8bdbe1766a3fad1c03059393a0f1f01839b19f98f235dc3b97bd
Deadline is 7/23/12 (11:59:59PM UTC-11). Here’s the Official Submission form. Good luck!!
Copyright 2012, Lake Missoula Group, LLC. All rights reserved.
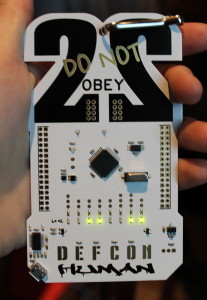
 If you grabbed a contest disc to play after DEFCON, here are the passwords you’ll need to mount the TrueCrypt volume for each round.
If you grabbed a contest disc to play after DEFCON, here are the passwords you’ll need to mount the TrueCrypt volume for each round.